May 12, 2026
Digital Rhetorical Privacy Collective
May 7, 2026, will long be remembered beyond the end of this spring semester. Not because of any major breakthrough in scientific discovery or even the legal restoration of millions in NEH grant funding previously cut by DOGE. Instead, many in education will remember it as the day their learning management system (LMS) went dark.
What Happened with Canvas?
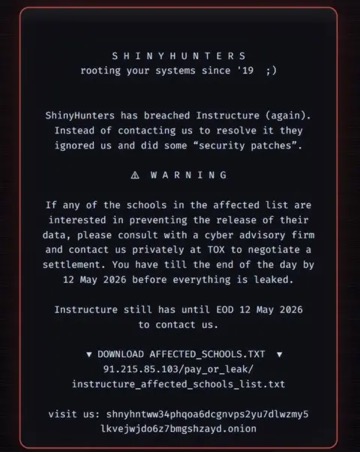
A major cybersecurity incident disrupted the Canvas LMS platform that is used by nearly 9,000 schools and universities worldwide. ShinyHunters, a “black hat” hacker group previously linked to breaches at AT&T, Ticketmaster, and ADT Security, claimed responsibility for breaching systems operated by Instructure, the company behind Canvas, and replacing portions of the login infrastructure. Students and faculty at higher education institutions and many K–12 districts reported being unable to access assignments, grades, or coursework during one of the busiest periods of the academic year. Instructure responded by temporarily placing portions of Canvas into maintenance mode––claiming it was “scheduled”––while investigators analyzed the attack and restored services. ShinyHunters then posted this ransom-style message demanding negotiations before May 12:
Online reports indicated the breach exposed names, email addresses, student ID numbers, and internal communications associated with millions of users globally. According to the AP, Canvas has millions of active users across nearly 9,000 institutions with billions of data points. The attackers claimed to possess data connected to roughly 275 million individuals. However, the full scope has not yet been verified. In response to the attack, Instructure stated that there is no evidence that passwords, financial information, Social Security numbers, or government IDs were compromised. Still, universities and school districts warned users to remain alert for phishing scams and suspicious activity. Schools across the globe began emergency response measures, including redirecting students to secondary systems, disabling integrations, and conducting security reviews while forensic investigations continued. Administrators also directed teachers to consider alternative modes for delivering and collecting final assignments. By May 8, Canvas access was partially restored, but many schools did not make it available for use immediately.
Why Does the Instructure Data Breach Matters?
Canvas, as the LMS with the most market share in the U.S., manages educational data at an astronomic scale. Not only are student assignments, grades, and messages maintained by the system, but every click on a link and minute spent on a page is monitored. Individually, these data points may seem insignificant, but in the aggregate, they represent untold amounts of knowledge and billions in corporate profit.
Ultimately, the Canvas data breach matters for educators and the public because the platform serves as critical infrastructure for modern education. Millions of students, teachers, professors, and administrators rely on Canvas LMS every day, and a disruption, especially during final exam season, immediately interrupts academic operations-as-usual at institutions around the world, delaying coursework, assessments, and graduation-related processes. Beyond downtime and perhaps more importantly, the possible exposure of student records and communications raises serious privacy and cybersecurity concerns because educational institutions often store sensitive personal information in centralized systems that students are required to use. We could see this, then, as a violation of the Family Educational Rights and Privacy Act (FERPA). Even if financial or government identification data was not confirmed stolen, compromised contact information and internal communications can be used to fuel phishing campaigns, identity fraud attempts, and social engineering attacks targeting students and faculty.
As Heather Hollingsworth has written for the AP, “Rich in digitized data, the nation’s schools are prime targets for far-flung criminal hackers, who are assiduously locating and scooping up sensitive files that not long ago were committed to paper in locked cabinet.” This is a line recycled from her reporting on a 2023 cyberattack. Institutions increasingly depend on cloud-based systems like Canvas for nearly every aspect of instruction, yet many schools lack the resources or cybersecurity staffing available to large corporations or government agencies. An incident affecting a single vendor can cascade across thousands of institutions simultaneously, creating operational, financial, and reputational damage on a global scale. The event is likely to increase pressure on education technology (Ed Tech) providers and universities to strengthen security practices, improve incident response planning, require stronger authentication protections, and reassess how student data is stored and shared across third- and fourth-party services. Will that pressure lead to significant change is another question.
What Can I Do??
Events like the Instructure/Canvas data breach implicate millions of actors (i.e., students, teachers, administrators, IT specialists, government officials, EdTech executives and product designers). As one node in an immense web, educators may feel helpless in the face of such an event. This alongside other frustrations with academic surveillance, censorship, and disinvestment make it difficult to not shrug off the data breach as a casualty of modern education and our digital lives. However, there are steps we can take! By way of conclusion, we highlight just three of many possible actions below.
Talk with Students about Data Ownership, Privacy, and Security:
Educators should approach conversations about the Canvas data breach as an opportunity to teach their students about practical digital citizenship and data privacy awareness. Teachers should explain that online platforms collect and store personal information to provide educational services, but that systems connected to the internet carry some level of cybersecurity risk. Students should understand what kinds of information may be involved in breaches, including names, email addresses, course activity, or messages, and why protecting personal data matters not only in educational contexts but public contexts, too. Educators should reinforce core data privacy principles including:
- minimizing the amount of personal information shared online
- using strong and unique passwords
- enabling multi-factor authentication when available
- recognizing phishing attempts that may follow a publicized breach
Framing the discussion with students around empowerment and informed decision-making, and not crisis and panic, helps them build long-term habits for protecting their digital identities across all platforms, not just the LMS they use at school.
Insist on Transparency and Responsible Technology Use in Classrooms:
Teachers and administrators should emphasize transparency, trust, and responsible institutional response is critical when data breaches occur. When discussing the Instructure/Canvas data breach, students and, in some cases, parents deserve clear communication about what occurred, what information may have been affected, what actions the institution or school district is taking, and what steps students themselves can take to stay safe. Here, educators in both higher education and at K-12 levels can model ethical data stewardship by discussing why schools have a responsibility to protect student information and why companies that manage educational technology must be held accountable for strong security practices. Ultimately, educators can help students become more thoughtful, privacy-conscious users of technology in both academic and personal settings by connecting the incident to real-world conversations about cybersecurity and personal rights.
Moreover, teachers and administrators need to be transparent and responsible about how and why we even use LMS systems like Canvas. On the surface, the convenience of the LMS is clear, and, certainly, many have been sold on the promise that the use of Ed Tech will improve learning outcomes and student performance (though that promise has had very little return on investment and now faces significant pushback). However, the true “value” of the LMS and many Ed Tech tools comes from its contribution to “accountability” logics. Namely, teachers can track student engagement with the LMS and posted materials and administrators can do the same with teachers. This tracking––good ol’ fashion surveillance––creates hierarchies of power that are not necessarily visible to LMS users, especially students. We need to take this moment to change that!
Reduce, Rethink, Refuse LMS Use:
This may be difficult, especially since LMSs are often mandated and, for-better-or-worse, do provide a level of centralized exchange that makes teaching and learning more convenient, but maybe it’s time to reduce and rethink (at minimum) or perhaps even refuse LMS use. Our dependence on data creating and data collecting technologies in education makes classrooms vulnerable. Canvas––just one of many Ed Tech companies–– has exclusive multi-year multi-million contracts with schools, universities, and even entire states. If this company can be hacked and its data archives ransomed, what confidence can we have with these technologies as tools for learning? Recent moves to reduce Ed Tech use and refuse GenAI integrations demonstrate opportunities for, if not disentangling ourselves completely, at least not adding to and simplifying the techno-infrastructures that hold up contemporary education. How to move forward is a pedagogical choice every teacher will need to make based on their specific institutional, technological, and ethical contexts.
Reduce:
- Ditch discussion board assignments and move to tools that might actually facilitate rich engagement (for examples: see Johnson and Smith, 2025)
- Provide content through alternative modes and trusted systems
- Only post what is mandated (many schools require that the LMS host the course syllabus and current grade information)
Rethink:
- For some, especially those teaching online, the LMS is the classroom. In these cases, rethinking how the LMS is used, what students know about the LMS data collection and vulnerabilities, and how embedded course analytics are engaged is vital.
Refuse:
- Make alternative environments that enhance student learning and displace danger of data surveillance and capture. This may be personal course websites or Discord channels, for example.
- Consider the value of low tech options! There is value in low/no tech teaching, but we caution that any decisions here be made for pedagogical reasons and not in the pursuit of “catching” GenAI use, etc.
- Work with colleagues and students to demand transparency and change from Ed Tech companies and the administrators who sign the contracts and mandate the use of certain tools.
While hackers may have temporarily pulled the plug on Canvas last week, it may be time that we consider our role in unplugging surveillance-based Ed Tech on a larger scale.

Leave a comment